Tata Consultancy Services official website www.tcs.com has been attacked and hacked. The hacker has left a message suggesting the website is up for sale.
At the time of writing of this post if you visited the official url of TCS, www.tcs.com; this is message you are greeted with.
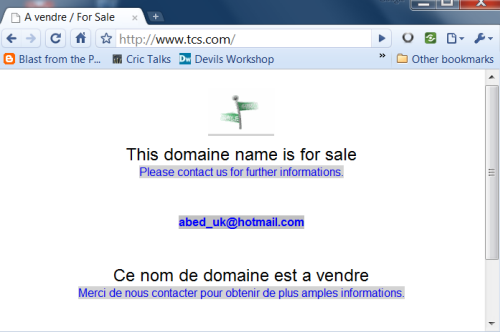
Strangely the hacker has put up a email Id out there in case someone is interested in buying the domain.
It is probably unrelated but there has been a rise in official websites being hacked into with messages. This is known as defacing homepages. Only recently Indian government had admitted that China based hackers had attacked official computers. But those were more sophisticated and meant to attack computer systems rather than deface any websites.
DNS Attack?
It seems TCS is facing DNS attack of some kind as the homepage opens fine with Pagewash. Here is a video to explain.
17 Comments
haha! lolzz
lolzzz. the hacker has also put up a visitor count icon on the hacked site 😛
@Rishabh: itz current online user’s count?
Wud I have been the hacker, I wud have put the company for Sale 😀
The site is back online and running.
The site is back up.
Site is not hacked rather DNS server that you are using is hacked.
[Disclaimer: I’m an employee of TCS, though I’m posting this in my personal capacity]
tcs.com was not hacked. What did happen was that the DNS records that supply the IP were reset to some other IP.
Whether that was done by actually hacking tracom/netsol or by social engineering a valid change request I do not know.
I know the site was fine because going through the internal DNS got me the correct IP address and the correct content.
I believe the problem started sometime before 1am IST [this is a wild guess, from other symptoms], and was resolved around noon or so [this guess is more accurate because I was semi-actively monitoring it].
In both instances, it would have taken a few hours for the bad data to expire from DNS caches. Depending on who your DNS provider is, you may have seen it “come back” at different times. If you were running your own DNS, you could have purged your DNS cache manually and would know more accurately when it came back (or just run a “dig +trace” at 10-minute intervals looking for the right IP to come back)
Regards,
Sitaram
@sitaram
Thanks Sitaram. This detailed info has completed the post now 🙂
@Sitaram: Thanks for the input and great insights. As vivek said, makes the post complete.
Thanks 4 d info. We were really confused about it. Now pretty clear 🙂
The site is back and running now.. I wonder what would be the next Target..
whatever may be the reason , this should not have happened for the india’s largest IT company
While it is obvious that this was a DNS redirect and not a website hack per se, what is not clear is why was TCS singled out for this attack. After all, whoever hacked NetSol’s DNS server could have wreaked havoc on many more domain names.
@mary:
try this google search http://www.google.co.in/search?q=but+the+reverse+is+vm2k3-web5.mgt.hosting.dc2.netsol.com&hl=en&filter=0
you’ll get about 160 hits, each containing some domain that was discovered to point to the same IP that tcs.com was directed to at that time.
Now add in the fact that this is only for vm2k3-web5 (whatever that means!) under dc2 (presumably some cluster in the DC area) and speculate how many more will turn up if you try other combinations of numbers, locations (ny, la, etc).
Count all of those and you’ve got your answer…
my 2 cents… 🙂
The site is back on its road i think so friend.